The problem
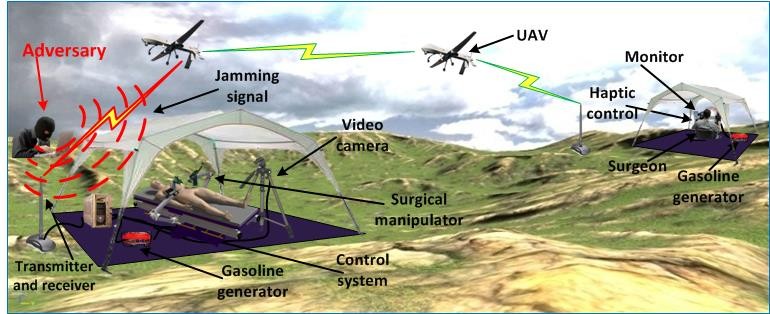
In telerobotic applications such as bomb disposal, search and rescue and robotic surgery, robots primarily serve as extensions of people. Human operators, often geographically distant, interact with robots through a communication channel. It is expected the next-generation teleoperated systems will combine the existing, publicly available networks with temporary ad-hoc wireless and satellite networks, to send audio, video and other sensory information to one or more remote operators. Surprisingly, the security vulnerabilities of these cyber-physical systems, and methods to prevent them or mitigate the effects of malicious hacking, have received little attention in the research community.
Our solution
This project is developing tools to prevent security threats in telerobotics, by monitoring and detecting malicious activities and correcting for them. To develop tools to prevent and mitigate security threats against telerobotic systems, this project adapts cybersecurity methods and extends them to cyber-physical systems. Knowledge about physical constraints and interactions between the cyber and physical components of the system are leveraged for security. A monitoring system is developed which collects operator commands and robot feedback information to perform real-time verification of the operator. Timely and reliable detection of any discrepancy between real and spoofed operator movements enables quick detection of adversarial activities. The results are evaluated on the UW-developed RAVEN surgical robot.
Impact
This project brings together research in robotics, computer and network security, control theory and machine learning, in order to gain better understanding of complex teleoperated robotic systems and to engineer telerobotic systems that provide strict safety, security and privacy guarantees. The results are relevant and applicable to a wide range of applications, including telerobotic surgery, search and rescue missions, military operations, underwater infrastructure and repair, cleanup and repair in hazardous environments, mining, as well as manipulation/inspections of objects in low earth orbit.
Affiliated Students and Faculty: Tamara Bonaci, Jeffrey Herron, Junjie Yan, Howard Chizeck, Blake Hannaford, Tadayoshi Kohno
Publications:
J. Yan, K. Huang, T. Bonaci, and H. J. Chizeck, ‘Haptic Passwords’, to be presented at the 2015 IEEE/RSJ International Conference on Intelligent Robots and Systems, September 2015, Hamburg, Germany
T. Bonaci, J. Herron, T. Yusuf, T. Kohno and H. J. Chizeck, ‘To Make A Robot Secure: An Experimental Analysis of Cyber Security Threats Against Teleoperated Surgical Robots‘, [arXiv: 1504.04339], April 2015
T. Bonaci, J. Yan, J. Herron, T. Kohno and H. J. Chizeck, ‘Experimental Analysis of Denial-of-Service Attacks on Teleoperated Robotic Systems‘, in the Proceedings of the 6th ACM/IEEE International Conference on Cyber-Physical Systems, April 2015, Seattle, WA
T. Bonaci, A. Alva, J. Herron, R. Calo, H. J. Chizeck, ‘I Did It My Way: On Law and Operator Signatures for Teleoperated Robots‘ to be presented at the 4th Annual Conference on Robotics, Law and Policy, Seattle, WA, April 2015
T. Bonaci, H. J. Chizeck, ‘On Potential Security Threats Against Rescue Robotic Systems’, the Proceedings of the 10th IEEE International Symposium on Safety, Security and Rescue Robotics, College Station, TX, November 2012
T. Bonaci, H. J. Chizeck, ‘Surgical Telerobotics Meets Information Security‘, the Proceedings of the Robotics, Science and Systems (RSS) Workshop on Algorithmic Frontiers in Medical Robotics: Manipulation in Uncertain, Deformable, Heterogeneous Environments, Sydney, Australia, July 2012
Presentations:
T. Bonaci, “Cyber Security for Teleoperated Roots in Smart Cities”, 2015 NSF Early-Career Investigators’ Workshop on Cyber-Physical Systems in Smart Cities, April 2015, Seattle, WA
H. J. Chizeck, T. Kohno, and T. Bonaci, ‘CPS Breakthrough: Secure Telerobotics’, 5th NSF Cyber-Physical Systems Principal Investigators’ Meeting, November 2014, Arlington, VA
T. Yusuf, T. Bonaci, T. Kohno, H. J. Chizeck, ‘“Dr. Hacker, I Presume?” An Experimentally-backed Discussion about Security of Teleoperated Surgical Systems‘, 2014 USENIX Summit on Health Information Technologies, San Diego, CA, August, 2014
Patents:
H. J. Chizeck, T. Bonaci, T. Lendvay, ‘Enhanced Safety and Security for Telerobotic Systems‘, US13/935,436, July 3, 2013
H. J. Chizeck, T. Bonaci, ‘Using Supplemental Encrypted Signals to Mitigate Man-in-the-middle Attacks on Teleoperated Systems‘, PCT/US2013/067528, October 30, 2013
Funding Sources:
